Hackers range from allies identifying system weaknesses to foes pilfering sensitive data. No system is perfect and completely secure. Identifying exploitable loopholes is the first step in protecting your system and hackers can help. How can you leverage hacking to protect your systems from infiltration by bad actors? This guide navigates the complex hacker ecosystem and suggests strategies you can use to fortify your company’s digital defenses.
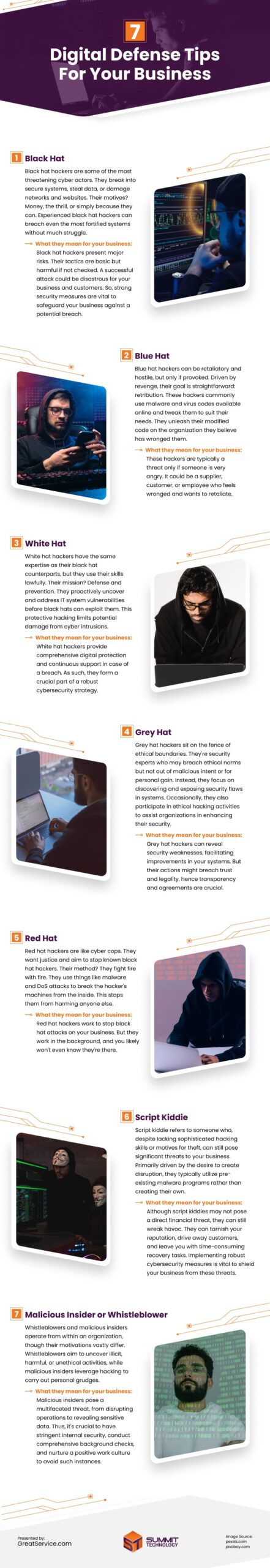
Black Hat
Black hat hackers are some of the most threatening cyber actors. They break into secure systems, steal data, or damage networks and websites. Their motives? Money, the thrill, or simply because they can. Experienced black hat hackers can breach even the most fortified systems without much struggle.
What they mean for your business: Black hat hackers present major risks. Their tactics are basic but harmful if not checked. A successful attack could be disastrous for your business and customers. So, strong security measures are vital to safeguard your business against a potential breach.
Blue Hat
Blue hat hackers can be retaliatory and hostile, but only if provoked. Driven by revenge, their goal is straightforward: retribution.
These hackers commonly use malware and virus codes available online and tweak them to suit their needs. They unleash their modified code on the organization they believe has wronged them.
What they mean for your business: These hackers are typically a threat only if someone is very angry. It could be a supplier, customer, or employee who feels wronged and wants to retaliate.
White Hat
White hat hackers have the same expertise as their black hat counterparts, but they use their skills lawfully. Their mission? Defense and prevention.
They proactively uncover and address IT system vulnerabilities before black hats can exploit them. This protective hacking limits potential damage from cyber intrusions.
Organizations like Google, Facebook, and Uber employ white hat hackers to safeguard their business systems. They even offer “bug bounties” for identifying critical system flaws.
What they mean for your business: White hat hackers provide comprehensive digital protection and continuous support in case of a breach. As such, they form a crucial part of a robust cybersecurity strategy.
Grey Hat
Grey hat hackers sit on the fence of ethical boundaries. They’re security experts who may breach ethical norms but not out of malicious intent or for personal gain. Instead, they focus on discovering and exposing security flaws in systems. Occasionally, they also participate in ethical hacking activities to assist organizations in enhancing their security.
What they mean for your business: Grey hat hackers can reveal security weaknesses, facilitating improvements in your systems. But their actions might breach trust and legality, hence transparency and agreements are crucial.
Red Hat
Red hat hackers are like cyber cops. They want justice and aim to stop known black hat hackers. Their method? They fight fire with fire. They use things like malware and DoS attacks to break the hacker’s machines from the inside. This stops them from harming anyone else.
What they mean for your business: Red hat hackers work to stop black hat attacks on your business. But they work in the background, and you likely won’t even know they’re there.
Script Kiddie
Script kiddie refers to someone who, despite lacking sophisticated hacking skills or motives for theft, can still pose significant threats to your business. Primarily driven by the desire to create disruption, they typically utilize pre-existing malware programs rather than creating their own.
Their usual attack mode is DDoS (Distributed Denial of Service) or DoS (Denial of Service). These methods overwhelm an IP address with high volumes of useless traffic until it crashes. The impact resembles the collapse of retail websites on peak sale days.
What they mean for your business: Although script kiddies may not pose a direct financial threat, they can still wreak havoc. They can tarnish your reputation, drive away customers, and leave you with time-consuming recovery tasks. Implementing robust cybersecurity measures is vital to shield your business from these threats.
Malicious Insider or Whistleblower
Whistleblowers and malicious insiders operate from within an organization, though their motivations vastly differ. Whistleblowers aim to uncover illicit, harmful, or unethical activities, while malicious insiders leverage hacking to carry out personal grudges.
A malicious insider might attack their own organization to highlight security gaps or take revenge for a denied raise by exposing confidential information. They may also divert payments or install spying malware on their colleagues’ systems.
What they mean for your business: Malicious insiders pose a multifaceted threat, from disrupting operations to revealing sensitive data. Thus, it’s crucial to have stringent internal security, conduct comprehensive background checks, and nurture a positive work culture to avoid such instances.
Verdict
Hackers exploit security gaps for various reasons. They use tools and tricks to access systems and retrieve data. To guard against them, antivirus software and unique passwords should be your first line of defense. Enabling two-factor authentication can also downsize the damage hackers can do by making it challenging to access your systems. Additionally, consider managed IT support, including a 24/7 security operations center (SOC), to continuously monitor and defend against cyber threats.
Infographic
In today’s digital realm, hackers range from those enhancing security to malicious actors seeking gain. Understanding these types is vital for strong defenses. Businesses must prioritize cybersecurity, employing tools like antivirus software and managed IT support. Proactive measures are key to safeguarding digital assets effectively.
Video