Due to digital transformation and the adoption of cloud tech, companies face greater risk than they did a decade ago. According to Check Point Research (CPR), the second quarter of 2022 saw worldwide cyber-attacks grow by 32% compared to Q2 2021, with the average weekly attacks per company hitting a peak of 1,200 attacks.
While many organizations are aware of the threats, the complex nature of attack vectors makes it difficult to develop an effective security strategy. And the fact that cybercriminals can strike at any time doesn’t make things any easier—especially for small businesses that lack the resources to monitor systems 24/7.
The good news is that a Security Operation Center (SOC) can help you take a layered approach to security, resulting in better protection of your data and processes.
What Is a Security Operations Center (SOC)?
A security operations center (SOC) is a command center for infosec professionals. People working within this center monitor, detect, and respond to security incidents that an organization may face. SOC personnel are self-sufficient with distinguished cybersecurity skills, though they may sometimes work with other departments or teams.
Most SOCs function 24/7, with staff members working in shifts to prevent intrusions and manage log activity. Essentially, SOCs aim to gain a comprehensive view of the company’s threat landscape, including endpoints, servers, applications, and networks. The 360-degree view helps them correctly exercise all security best practices and workflows.
Advantages of a Security Operations Center
By implementing a SOC in your business, you can take advantage of the following benefits:
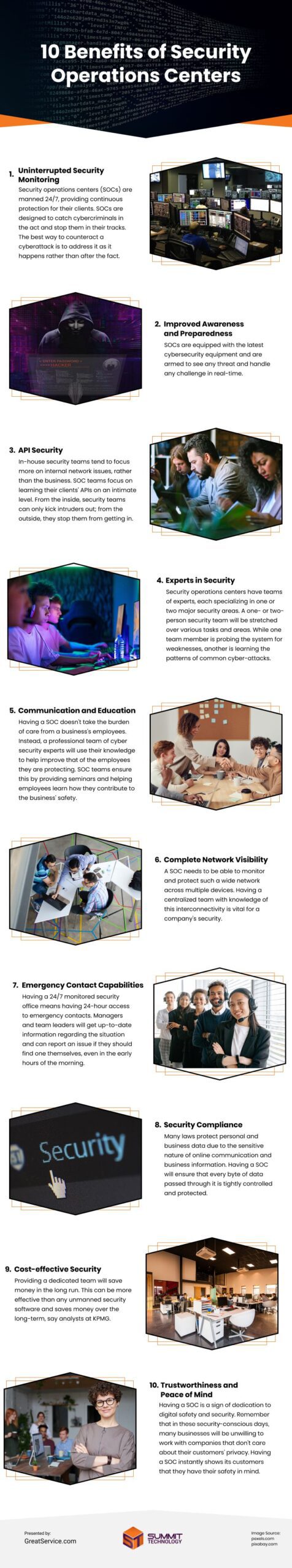
Uninterrupted Security Monitoring
Threats to online security do not operate according to working hours. Cybercriminals exist worldwide and can target their victims at any time.
Security operations centers are manned 24/7, providing continuous protection for their clients. The best way to counteract a cyberattack is to address it as it happens rather than after the fact. SOCs are designed to catch cybercriminals in the act and stop them in their tracks.
Improved Awareness and Preparedness
SOCs are not one man sitting at a computer in his home. They are an organized workspace of trained professionals with a broad range of expertise who are prepared to face any task.
Operatives are equipped with the latest cybersecurity equipment, meaning they are armed to see any threat and handle any challenge.
API Security
Every business uses its own application programming interfaces (APIs) depending on its needs. In-house SOC teams tend to focus more on internal network issues, protecting individual network setups, rather than the business.
SOC teams, by contrast, focus on learning their clients’ APIs on an intimate level. This provides them with the knowledge and awareness necessary to help them work both within and outside the business. From the inside, security teams can only kick intruders out. From the outside, they stop them from getting in.
Experts in Security
A one- or two-person security team will be stretched over various tasks and areas. However, there are so many cyberattacks that a jack-of-all-trades just won’t cut it.
Security operations centers have teams of experts, each specializing in one or two major security areas. While one team member is probing the system for weaknesses, another is learning the patterns of common cyber-attacks to create countermeasures.
Communication and Education
Having a SOC doesn’t take the burden of care from a business’s employees. Instead, a professional team of cyber security experts will use their knowledge to help improve that of the employees they are protecting.
After all, the best way to prevent security attacks is to ensure that those using the system know how to do so safely. SOC teams ensure this by providing seminars and helping employees learn how they contribute to the business’ safety.
Complete Network Visibility
Since the world has embraced the remote office, networks have been stretched thin over wide and unpredictable areas. Having a handful of people working in an office, some working from home, and a few more working from their phones is a cybersecurity nightmare. Luckily, a good SOC can monitor and protect such a wide network across multiple devices. A centralized team with knowledge of this interconnectivity is vital.
Emergency Contact Capabilities
Having a 24/7 monitored security office means having 24-hour access to emergency contacts. In the event of a large cyberattack, SOC teams will be easy to reach while they handle the situation. Managers and team leaders will get up-to-date information regarding the situation and can report an issue if they should find one themselves, even in the early hours.
Security Compliance
Many laws protect personal data due to the sensitive nature of online communication and business information. Since businesses handle this precious data daily, several laws must be strictly adhered to.
Having a SOC team will cover most businesses for the compliance laws they must follow. With a security operations center, every byte of data passed through the business will be tightly controlled and protected.
Cost-effective Security
Providing a dedicated team will save money in the long run. By ensuring that the business is prepared for any cyberattack, there will be few instances of them happening. This can be more effective than any unmanned security software and saves money in the long run.
Trustworthiness and Peace of Mind
Having a SOC is a sign of dedication to digital safety and security. Any company that hires a SOC instantly shows its customers that they care and have their safety in mind, boosting its trustworthiness. Remember that in these security-conscious days, many businesses will be unwilling to work with companies that do not take their privacy seriously.
How to Get Managed SOC For Your Business
Great Service offers managed IT services that includes a 24/7 Security Operations Center. Our SOC team solely focuses on analyzing and monitoring your company’s security. This helps us proactively defend your organization against cyber threats.
Infographic
Companies now confront higher risks than they did ten years ago because of digital transformation and the use of cloud technology. The good news is that a Security Operation Center (SOC) can assist you in adopting a layered security strategy, improving the security of your data and business operations. SOC professionals are self-sufficient and possess exceptional cybersecurity abilities.
Video